
21 Apr Cybersecurity Audit Miami: The 2026 Strategic Guide for Business Protection
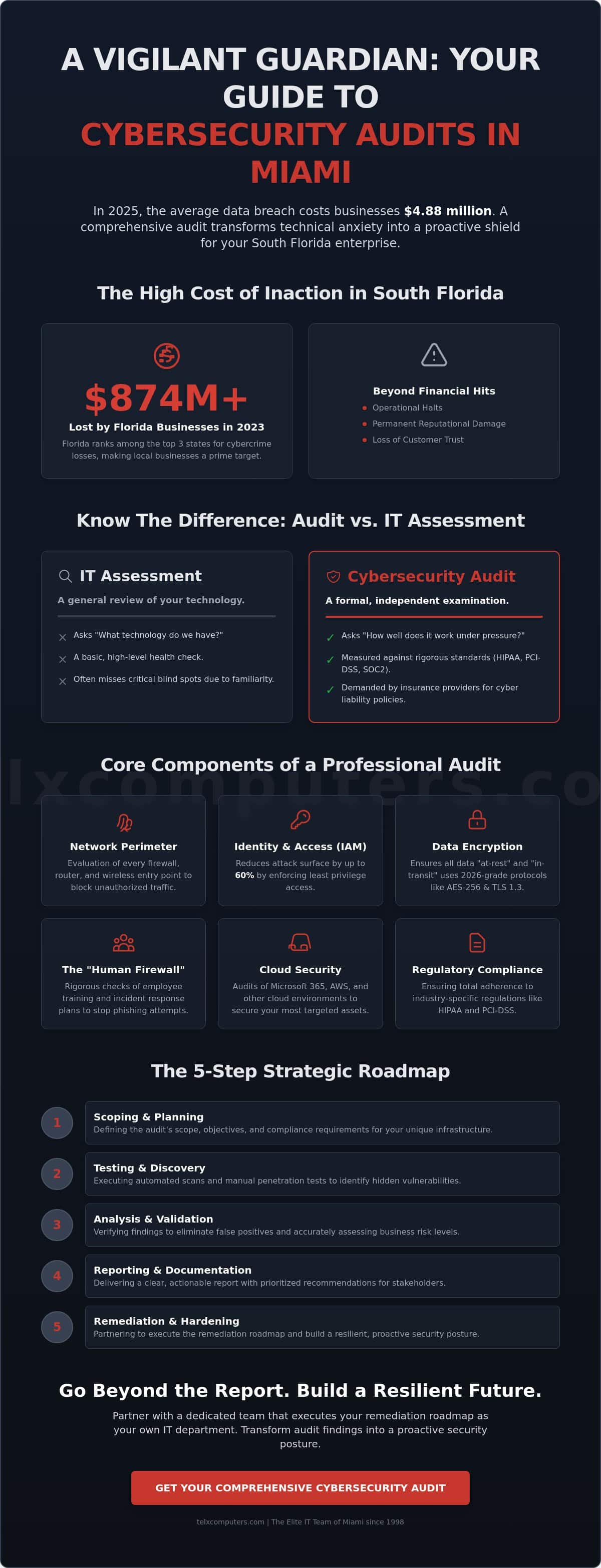
According to the 2025 IBM Cost of a Data Breach Report, the average financial impact of a security failure has surged to $4.88 million, a 10% increase over the previous year. What if a single overlooked vulnerability in your hybrid work setup is all it takes to halt your South Florida operations? You likely already feel the pressure of evolving ransomware threats and the confusion of meeting strict HIPAA or PCI-DSS requirements. It’s overwhelming. A professional cybersecurity audit Miami removes this uncertainty by transforming your technical anxiety into a proactive shield for your enterprise.
This guide provides a clear roadmap to identify hidden security gaps and secure the documented proof of protection required by insurance providers and partners. We’ll show you how a comprehensive assessment ensures total regulatory compliance while building a resilient infrastructure. You’ll gain the strategic insights needed to achieve total peace of mind. Your business deserves a vigilant guardian that stays one step ahead of the threats.
Key Takeaways
- Secure your South Florida operations by understanding how a comprehensive cybersecurity audit Miami identifies hidden vulnerabilities and ensures total regulatory compliance.
- Learn to distinguish between automated vulnerability scans and deep-dive technical assessments to choose the most resilient protection for your unique infrastructure.
- Master the five-step strategic roadmap designed to scope, test, and harden your network against the sophisticated ransomware threats of 2026.
- Discover how to transform audit findings into a proactive security posture by partnering with a dedicated team that executes your remediation roadmap as your own IT department.
What is a Cybersecurity Audit and Why Does Your Miami Business Need One?
A Information security audit is a comprehensive, independent evaluation of your company’s IT infrastructure, security policies, and internal controls. It isn’t just a basic checkup. It’s a deep dive into the digital architecture that keeps your business running. For local firms, a cybersecurity audit Miami professionals conduct ensures that every layer of your defense is solid and compliant with 2026 standards.
To better understand how these evaluations function within an organization, watch this helpful video:
Internal self-checks often miss the blind spots that an “Expert Guardian” from a third-party firm will catch. These external audits provide an unbiased perspective that your internal team might overlook due to familiarity. Miami’s position as a hub for international trade makes it a prime target for data theft and sophisticated ransomware attacks. We’ve seen that a secure digital posture directly impacts business valuation. Whether you’re a startup looking for venture capital or an enterprise preparing for an acquisition, your cybersecurity health is a primary metric for investors.
The High Cost of Inaction in South Florida
Florida consistently ranks among the top three states for cybercrime losses. According to the FBI’s 2023 Internet Crime Report, Florida businesses lost over $874 million to digital fraud. A data breach is more than a financial hit; it stops the silent engine of your operations. In Miami’s tight-knit business community, news of a breach travels fast. Reputational damage can be permanent, leading to a loss of trust that takes years to rebuild. We focus on ransomware protection to ensure your business stays online and your reputation remains intact.
Cybersecurity Audit vs. IT Assessment
Many owners confuse an IT assessment with a formal audit. An assessment is a general review of your technology. In contrast, an audit is a formal examination measured against specific, rigorous standards like SOC2 or HIPAA. By 2026, insurance providers have shifted. They now demand these formal audits before issuing or renewing cyber liability policies. A cybersecurity audit Miami is a rigorous diagnostic of digital health. It moves beyond “what we have” to “how well it actually works” under pressure. Choosing managed IT support services that include these audits ensures your compliance is never in question.
Core Components of a Professional Cybersecurity Audit
A comprehensive cybersecurity audit Miami companies rely on goes far beyond a simple software scan. It begins with a deep dive into your network perimeter. We evaluate every firewall, router, and wireless entry point in your Miami or Aventura office to ensure no legacy ports remain open to attackers. Modern threats move fast; therefore, your hardware must be configured to block unauthorized traffic before it ever touches your internal servers.
Identity and Access Management (IAM) serves as the next pillar of your defense. We audit exactly who holds the keys to your sensitive data and verify the business necessity for that access. Aligning your internal controls with the Cybersecurity Performance Goals established by CISA ensures your organization meets a high baseline of protection. This process removes “ghost accounts” and enforces the principle of least privilege, which reduces your attack surface by up to 60%.
Data encryption standards have shifted significantly. We confirm that all “at-rest” and “in-transit” data utilizes 2026-grade protocols. If your sensitive files aren’t protected by AES-256 or TLS 1.3, they’re essentially sitting in plain sight. Finally, we review your “human firewall.” This involves a rigorous check of employee handbooks and incident response plans to ensure your staff can identify a phishing attempt within seconds of it hitting their inbox.
Technical Infrastructure and Cloud Security
Your cloud environment is often the first target for modern hackers. We audit Microsoft 365, AWS, and Azure configurations to close common leaks that expose internal files to the public web. Our team evaluates your hardware health through advanced server monitoring systems to prevent unexpected downtime. We also secure endpoints for remote teams working in Fort Lauderdale, ensuring their home networks don’t become backdoors into your corporate environment.
Physical Security and Disaster Recovery
Effective security includes the physical world. We assess on-site server room access and environmental controls to prevent unauthorized tampering or hardware failure. In South Florida, hurricane readiness is a non-negotiable part of your business strategy. We integrate cybersecurity with robust data backup solutions to ensure your operations remain resilient during regional power outages. Our experts verify the integrity of your hardware and provide comprehensive computer IT services to keep your local infrastructure optimized and secure.
If you haven’t reviewed your protocols since 2024, your business is likely facing invisible risks. You can get a clear picture of your current standing by requesting an instant quote for a professional assessment today.
Vulnerability Scans vs. Penetration Tests vs. Full Audits
A cybersecurity audit Miami isn’t a one-size-fits-all product. It’s a strategic process. Understanding the difference between scanning, testing, and auditing is vital for South Florida business owners who want to move beyond basic compliance toward true resilience. We categorize these services by their depth and intent to ensure you aren’t paying for a “smoke detector” when you actually need a “building inspector.”
- Vulnerability Scanning: This is your automated smoke detector. It runs 24/7 or on a schedule to identify known security holes, such as unpatched software or open ports. It’s fast and broad but doesn’t tell you if a hole is actually exploitable.
- Penetration Testing: This is the ethical hacker approach. A specialist actively tries to break into your systems to see how far they can get. If the scan finds an unlocked door, the pen tester walks through it to see if they can reach your sensitive client data.
- Cybersecurity Audit: This is the building inspector approach. It’s the most comprehensive level of protection. It evaluates your technical controls, your staff’s behavior, and your written policies against a formal framework.
When to Choose Which Service
A small boutique firm in Aventura with 15 employees has different needs than a 500-person enterprise in downtown Miami. For smaller teams, quarterly vulnerability scans are the baseline requirement to stay ahead of automated botnets. Larger organizations, especially those in finance or legal sectors, require annual penetration tests to meet 2025 compliance standards. These services shouldn’t exist in a vacuum; they must layer together to create a cohesive network IT support strategy. We recommend a 90-day cycle for automated scans and a full 12-month cycle for deep-dive audits to maintain a proactive defense posture.
The Limitations of Automated Scans
Software tools are excellent for speed, but they lack the intuition to spot “logical flaws.” A scan might see that a user has access to a specific folder and report it as “correct” because the permissions are technically valid. However, a human auditor will realize that a receptionist shouldn’t have access to the company’s payroll server. According to the 2024 Verizon Data Breach Investigations Report, 68% of breaches involved a human element, such as social engineering or privilege misuse, which automated tools often overlook. Human experts are essential for interpreting “false positives” that can waste your internal team’s time. Automation finds the cracks, but auditors find the cause. To understand the rigorous standards of a full review, the Cybersecurity Program Audit Guide provides a blueprint for how technical controls must align with management policies to be effective. Relying solely on “set it and forget it” software leaves your business vulnerable to the very human errors that drive modern cybercrime.
The 5-Step Process: What to Expect During a Miami Cybersecurity Audit
A professional cybersecurity audit Miami doesn’t have to be an intrusive or intimidating experience. At Telx Computers, we’ve refined a systematic approach that provides maximum visibility into your vulnerabilities while maintaining the flow of your business. We act as your Expert Guardian, transforming technical gaps into a fortified defense strategy. Our process follows five distinct phases designed for the high-stakes South Florida business environment.
- Phase 1: Discovery and Scoping. We begin by defining the exact boundaries of the audit. Our team identifies your most critical assets, from proprietary client databases to financial records, ensuring no part of your infrastructure remains unexamined.
- Phase 2: Data Collection and Testing. This is the technical deep dive. We utilize advanced tools to probe your network for weaknesses. By January 2026, 68% of South Florida enterprises have faced at least one sophisticated phishing or ransomware attempt; we simulate these real-world threats to see how your system holds up.
- Phase 3: Analysis and Risk Mapping. We don’t just hand you a list of bugs. We categorize every vulnerability by its potential impact on your operations. This allows you to see which risks require immediate intervention and which are lower priority.
- Phase 4: Reporting and Debriefing. We present our findings in a clear, non-jargon format. We sit down with your stakeholders to explain the logic behind our technical findings, linking them directly to your business outcomes.
- Phase 5: Remediation Roadmap. The audit concludes with a prioritized list of fixes. You get a step-by-step guide to securing your operations, moving your business from a state of vulnerability to a state of total proactive defense.
Navigating Local and Industry Compliance
Compliance is a moving target in 2026. Our audits specifically address the nuances of healthcare IT services, ensuring your practice meets every HIPAA requirement to avoid devastating fines. For law firms in Miami, we focus on client confidentiality and the strict ethical standards required for digital case files. We also ensure your business aligns with the latest 2026 Florida Digital Bill of Rights updates, which mandate strict data handling protocols for any entity operating within the state.
Minimal Disruption to Your Daily Operations
We understand that downtime is not an option. Telx Computers conducts the majority of the data collection phase through remote monitoring tools that run silently in the background. Your team won’t experience lag or system freezes while we work. When physical inspections are necessary, we schedule on-site visits for Miami and Fort Lauderdale offices during your off-peak hours. It’s a seamless integration of security and productivity that allows you to focus on growth while we handle the technical heavy lifting.
Ready to secure your South Florida business with a comprehensive assessment? Schedule your expert cybersecurity audit Miami today to protect your future.
Beyond the Report: Remediation and Proactive Security with Telx Computers
A cybersecurity audit Miami provides the blueprint for your defense, but the real work starts after the final page is read. IBM’s 2024 Cost of a Data Breach Report shows the average cost of a breach reached $4.88 million. Simply identifying vulnerabilities doesn’t stop attackers; closing those gaps does. Telx Computers functions as your integrated IT department, taking that remediation roadmap and turning it into a fortified defense. We don’t just hand you a list of problems. We fix them.
Transitioning to managed IT support shifts your business from a state of constant firefighting to one of prepared resilience. Instead of waiting for a 2026 audit to reveal new threats, our team monitors your systems 24/7. This proactive stance builds a security-first culture where every employee understands their role in protecting the company’s digital assets. It changes the conversation from “what went wrong” to “how we’re staying ahead.”
- Immediate Gap Closure: We prioritize high-risk vulnerabilities found in the audit to prevent exploitation.
- Internal Integration: We work as your team, not just a third-party vendor.
- Continuous Monitoring: Real-time threat detection replaces annual panic.
Strategic Partnership for Long-Term Growth
Audit data shouldn’t sit in a drawer; it should drive your long-term strategy. By leveraging these insights, businesses make smarter investments in their infrastructure through tailored IT outsourcing services. Our Expert Guardian approach means we’re always watching, ensuring your technology scales alongside your growth. This level of diligence does more than protect data. It can lower cyber insurance premiums by up to 25% in specific sectors and strengthens trust with your global partners. You gain a competitive edge by being the most secure link in the supply chain.
Get Started with a Miami Cybersecurity Specialist
Stop worrying about what you might’ve missed. Move from uncertainty to absolute confidence with a team that knows the South Florida landscape. We back our services with a guarantee of reliability that ensures your business stays operational and secure. Our specialists handle the technical complexity so you can focus on your core operations. Don’t wait for a breach to realize you’re vulnerable. Get an instant quote for your Miami cybersecurity audit today.
Take Command of Your Digital Defense for 2026
The threat landscape in South Florida evolves rapidly. Waiting for a breach to occur isn’t a strategy; it’s a liability. A comprehensive cybersecurity audit Miami ensures your infrastructure meets CISA-level standards while identifying hidden vulnerabilities that basic scans often miss. By integrating 24/7 proactive monitoring with a clear remediation roadmap, you transform your IT from a cost center into a resilient shield. Telx Computers acts as your dedicated IT department, providing fixed-price unlimited support plans that eliminate technical anxiety. You gain the stability needed to scale your business without the constant fear of downtime or data loss. Our team brings the expertise required to navigate the complex regulatory environment of 2026. Don’t leave your assets to chance when you can secure them with a partner who prioritizes your uptime.
Secure Your Miami Business with a Professional Cybersecurity Audit
We’re ready to help you build a safer, more profitable future for your organization.
Common Questions About Cybersecurity Audits
How much does a cybersecurity audit cost for a Miami business?
Professional assessments generally range from $5,000 to $15,000 for small enterprises, while complex environments may exceed $30,000 based on the 2024 Cost of Cybercrime report. Your final investment depends on the number of endpoints and specific compliance requirements. We focus on delivering a high return on security by identifying gaps before they become expensive breaches. This proactive approach ensures your budget protects your most valuable digital assets.
How long does a typical cybersecurity audit take to complete?
A standard cybersecurity audit Miami businesses undergo typically takes between two and six weeks to complete. The first 10 days involve data collection and technical scans of your network. We then spend the remaining time analyzing results and building your strategic roadmap. This timeline ensures we don’t disrupt your daily operations while maintaining a vigilant eye on your infrastructure’s integrity.
Is a cybersecurity audit the same as a HIPAA compliance check?
A cybersecurity audit is a broad evaluation of your entire IT infrastructure, whereas a HIPAA compliance check specifically targets the protection of health data under the 1996 federal law. While they overlap, a general audit might miss the 18 specific identifiers required for healthcare privacy. We integrate these standards into our partnership to ensure your medical practice meets every regulatory mandate without exception.
Can a small business in Miami perform their own cybersecurity audit?
Small businesses can perform basic internal reviews using the NIST Cybersecurity Framework, but they often lack the specialized tools required for deep penetration testing. 60% of small firms that experience a data breach go out of business within six months, according to the National Cyber Security Alliance. Professional oversight provides the objective validation your internal team needs to stay secure against sophisticated threats.
What is the difference between a SOC 2 audit and a general cybersecurity audit?
SOC 2 is a formal reporting standard governed by the AICPA that focuses on five trust service criteria, while a general audit is a flexible assessment of your security posture. A general audit identifies technical holes in your daily operations. A SOC 2 report proves to your clients that you’ve maintained these standards over a 12 month period. It’s a critical tool for B2B companies.
How often should my South Florida company undergo a professional audit?
You should schedule a professional audit at least once every 12 months or whenever you implement major infrastructure changes. The 2026 threat landscape evolves daily, making annual checks the bare minimum for South Florida companies. If you’ve added more than 15% new remote staff or migrated to a new cloud provider, an immediate review is the most proactive way to prevent security gaps.
Will a cybersecurity audit help me get lower cyber insurance rates?
Completing a professional audit can help lower your premiums by 10% to 25% according to industry data from major insurance providers. Carriers now require proof of multi-factor authentication and regular vulnerability scans before they’ll issue a policy. We act as your strategic ally by providing the documentation underwriters need to verify your risk profile is low and your business is reliable.
What happens if the audit finds major vulnerabilities in my network?
If we identify critical risks, we prioritize them into an immediate remediation plan based on their potential impact. We don’t just hand you a list of problems; we work as your IT department to patch holes and update configurations. Resolving a high-risk vulnerability within 24 hours can prevent the average $4.45 million cost associated with modern data breaches, ensuring your business remains resilient.

