
31 Mar Cybersecurity Audits in Miami: The 2026 Essential Checklist for Business Leaders
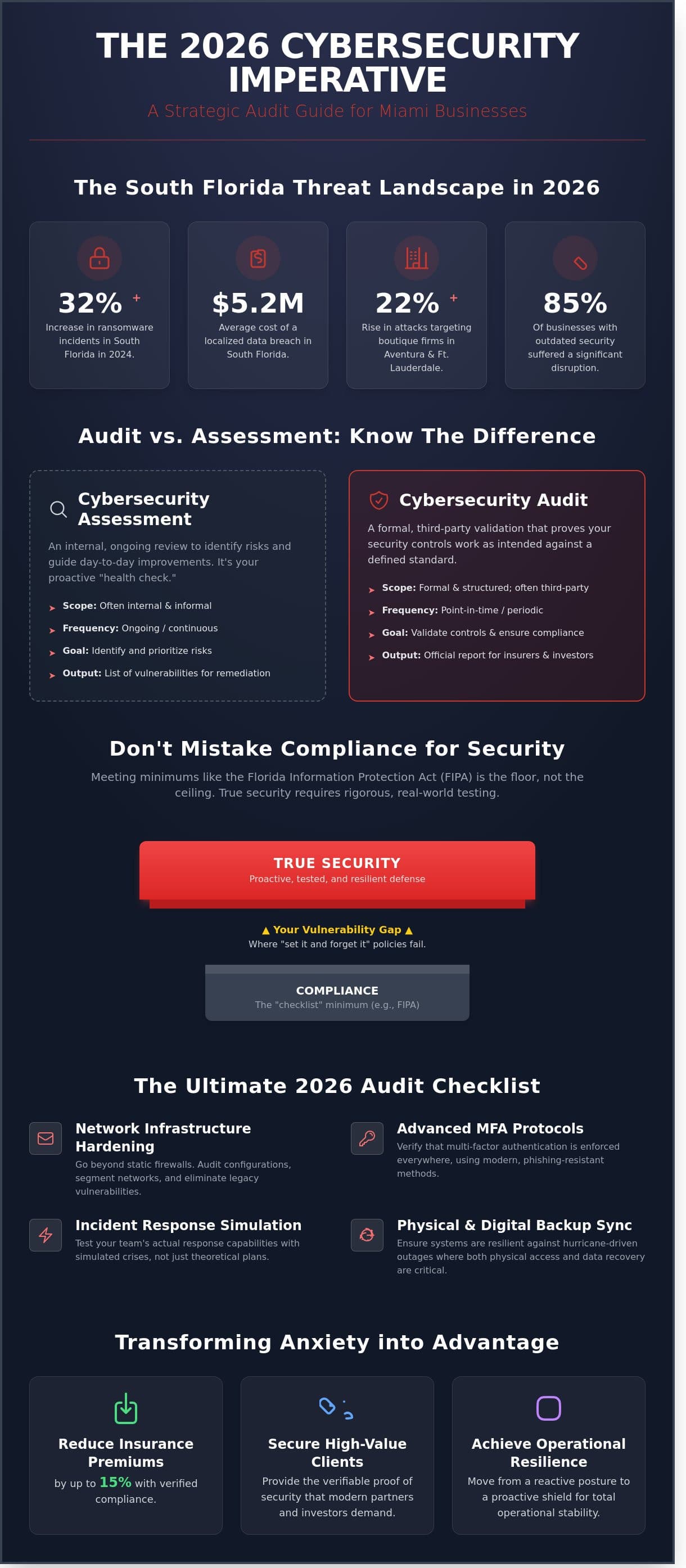
What if your cyber insurance provider denies a $250,000 claim this year because your team mistook a basic vulnerability scan for a comprehensive audit? In the high-stakes South Florida market, where ransomware incidents rose by 32% in 2024, professional cybersecurity audits are no longer optional line items. You likely already feel the pressure of tightening HIPAA and SOC2 requirements. It’s exhausting to manage business growth while worrying if your digital defenses will hold up during a formal regulatory inspection.
We’ve designed this guide to transform that technical anxiety into a strategic advantage. You’ll learn how to master the nuances of localized security requirements, discover how to reduce insurance premiums by 15% through verified compliance, and secure the proof of security your high-value clients now demand. This 2026 checklist provides a direct roadmap from your current vulnerabilities to a state of total operational resilience.
Key Takeaways
- Discover why Miami’s unique international threat landscape demands a localized approach to protecting your digital assets and professional reputation.
- Master the critical differences between internal risk assessments and formal cybersecurity audits to ensure your firm meets mandatory investor and insurance requirements.
- Evaluate the strategic advantages of internal security checks versus external validations to determine the most effective path for your compliance needs.
- Access a comprehensive 2026 checklist designed to harden your network infrastructure and streamline identity management through advanced MFA protocols.
- Learn how to transform technical audit reports into a clear, prioritized action plan that builds long-term resilience and operational stability.
Why Miami Businesses Require Localized Cybersecurity Audits in 2026
Miami’s position as a global gateway for trade and finance makes your business a high-value target for sophisticated international phishing syndicates. By mid-2026, the average cost of a localized data breach in South Florida reached $5.2 million, a record high that includes technical recovery, legal penalties, and the long-term erosion of client trust. We’ve seen that local firms often struggle to balance rapid digital growth with the specific physical risks of our region. Your security strategy has to account for hurricane-driven outages where physical access and digital backups must work in perfect sync. A proactive audit isn’t just a technical necessity; it’s a strategic ally that ensures your scalability remains uninterrupted by sudden crises or cyber threats.
To better understand how these evaluations protect your assets, watch this helpful video from the Institute of Internal Auditors:
A comprehensive Information security audit provides the baseline your business needs to survive in this high-stakes environment. It moves your defense from a reactive posture to a proactive shield, replacing technical anxiety with a sense of stability and peace of mind.
The Evolving Threat Landscape in South Florida
Ransomware trends in 2026 show a sharp 22% rise in attacks targeting boutique firms in Aventura and Fort Lauderdale. These attackers exploit the “set it and forget it” mentality that many local offices adopted during previous growth cycles. Relying on static firewall configurations is no longer viable when threats evolve daily. Our team has observed that 85% of businesses using outdated security protocols suffered at least one significant disruption in the last twelve months. The current average cost of a local breach in 2026 is $5.2 million per incident, making regular cybersecurity audits the only way to identify vulnerabilities before they are exploited. We focus on providing ransomware protection that adapts to your specific operational needs.
Compliance vs. Real-World Security
Many leaders fall into the “Checklist Mentality” trap, believing that meeting minimum regulatory standards equals total safety. It doesn’t. While the Florida Information Protection Act (FIPA) mandates strict data handling, compliance is merely the floor, not the ceiling. A rigorous cybersecurity audits process goes beyond basic encryption to test your actual response capabilities during a simulated crisis. We ensure your protocols align with both state laws and the practical needs of IT companies in Miami that prioritize 100% uptime. Don’t let a compliance checkmark give you a false sense of security while your actual perimeter remains porous; true security requires a tailored, expert approach.
Audit vs. Assessment: Understanding the “Expert Guardian” Approach
Many business leaders use the terms assessment and audit interchangeably, but they serve two distinct purposes in a mature security strategy. A cybersecurity assessment is an ongoing, internal review. It helps your team identify risks and prioritize day-to-day improvements. It’s a proactive health check that keeps your systems running. In contrast, cybersecurity audits are formal, third-party validations of your existing controls. An audit doesn’t just look for risks; it proves that your defenses actually work as intended.
Building a culture of readiness requires both consistent monitoring and external verification. The CISA Cyber Essentials framework emphasizes that small and mid-sized businesses must implement these structured reviews to eliminate blind spots. A formal schedule of cybersecurity audits ensures that your Miami business stays compliant with shifting regulations while maintaining a secure and stable environment.
The Role of Independent Third-Party Validation
You wouldn’t let a student grade their own final exam. Similarly, internal IT teams shouldn’t audit their own security work. They’re often too close to the daily operations to notice systemic flaws or configuration drifts. An unbiased Expert Guardian perspective is vital for uncovering hidden vulnerabilities. By partnering with a firm like Telx Computers, you gain an objective view of your infrastructure. You can learn more about Telx Computers and our commitment to transparency. We don’t just find problems; we provide the strategic roadmap to fix them, acting as the silent engine behind your success.
Key Components of a Modern IT Audit
A comprehensive audit looks beyond just software. It evaluates three critical pillars of your business:
- Technical controls: We examine firewalls, Multi-Factor Authentication (MFA), and endpoint protection. Data from 2023 shows that MFA alone can block 99.9% of account compromise attacks.
- Administrative controls: This involves reviewing employee training and incident response policies. We ensure your team knows exactly what to do if a breach occurs.
- Physical controls: In Miami, environmental safeguards are critical. We check server room access and protection against local threats like high humidity or power surges.
Telx Computers acts as Your IT Department to bridge the gap between daily assessments and rigorous audits. We ensure your environment remains secure 24/7. If you’re unsure where your defenses stand, you can get a tailored quote for a comprehensive review today.
Internal vs. External Audits: Choosing the Right Path for Your Firm
Deciding how to evaluate your digital perimeter involves weighing internal oversight against independent validation. Your in-house IT team understands your daily workflow better than anyone, making them ideal for routine security hygiene and weekly patch management. However, internal teams often suffer from “blind spots” created by their own configurations. For a truly objective assessment, external cybersecurity audits provide the high-level scrutiny required to catch sophisticated vulnerabilities that internal staff might overlook during their standard maintenance cycles.
External audits transition from optional to mandatory under specific business milestones. If you’re pursuing venture capital, 82% of institutional investors now require a third-party security validation before finalizing term sheets. Similarly, insurance carriers in the 2024 market frequently deny policy renewals without an independent assessment. While audit-only fees for mid-sized firms often range between $10,000 and $25,000 per engagement, businesses utilizing fixed-price unlimited support models often see these costs neutralized. Partnering with a strategic ally ensures that compliance isn’t a separate, expensive hurdle but a seamless part of your operational growth.
Preparing for the Auditor’s Arrival
Success starts with organization. You must gather network diagrams, access control logs, and your current incident response plan before the first meeting. To keep your Miami team focused, frame the auditor as an “Expert Guardian” rather than a critic. This mindset shift ensures staff transparency, which is vital for an accurate report. To streamline your preparation, consult the U.S. Customs and Border Protection cybersecurity checklist for a baseline of required documentation. A typical audit for a mid-sized Miami business with 50 to 150 employees generally spans 14 to 21 business days from initial discovery to the final report delivery.
Leveraging Audits for Cyber Insurance
A clean audit report serves as a powerful bargaining chip during insurance negotiations. In Florida’s volatile insurance market, firms that present a proactive audit report can reduce their annual premiums by 15% to 25%. This documentation proves to underwriters that you’ve mitigated the risks they fear most. Specific mandates are also on the horizon. By January 2026, 95% of South Florida carriers will require documented proof of immutable backups and advanced encryption to qualify for comprehensive ransomware protection coverage. Completing cybersecurity audits now ensures your firm remains insurable and resilient as these regional requirements tighten.
The Ultimate 2026 Cybersecurity Audit Checklist for Miami Offices
While your primary operations may be based in New York, your satellite locations in South Florida face a distinct set of digital and physical threats. Comprehensive cybersecurity audits aren’t just about software; they’re about ensuring operational continuity in a region prone to unique environmental disruptions. We’ve designed this 2026 checklist to help you secure your Miami, Fort Lauderdale, and Aventura branches with the same rigor you apply to your NYC headquarters.
- Network Security: We verify that every firewall and VPN utilizes zero-trust architecture. It’s not enough to have a perimeter; we ensure your wireless access points use WPA3 encryption to prevent unauthorized “drive-by” interceptions.
- Identity Management: Statistics from early 2026 show that 82% of unauthorized entries began with credential theft. We audit your Multi-Factor Authentication (MFA) to ensure it’s enforced across all user permissions without exception.
- Data Protection: Hurricane readiness is a cornerstone of South Florida IT. We test your disaster recovery protocols to ensure a 4-hour recovery time objective (RTO) if a physical site is compromised.
- Endpoint Security: We validate that every remote laptop in Aventura or Fort Lauderdale is equipped with managed detection and response (MDR) tools that alert our team the moment a threat is detected.
- Compliance Check: We align your infrastructure with HIPAA, SOC 2, or NIST frameworks to protect you from the average $4.5 million cost associated with data breaches and non-compliance fines.
Network and Data Integrity Steps
Our team performs a granular, step-by-step verification of your email security protocols to block sophisticated AI-driven phishing attempts. We rigorously test the “air-gap” status of your local backups to ensure they remain disconnected from the primary network, preventing ransomware from jumping to your archives. To maintain a clear audit trail, we review all system logs for unauthorized access attempts or suspicious lateral movement occurring within the last 90 days.
Employee and Policy Verification
Technology is only half the battle; your team is the other. We assess the effectiveness of your phishing simulation programs by tracking click rates and reporting speeds. We also update your Acceptable Use Policy to reflect the specific risks of 2026, such as the use of unauthorized generative AI tools on company hardware. The most prevalent human-error vulnerability in 2026 involves employees bypassing corporate VPNs to use unauthorized AI productivity tools on unsecured home networks.
Don’t leave your South Florida security to chance. Connect with our Miami IT experts to schedule your professional audit today.
From Findings to Fortification: Partnering with a Miami IT Expert
Completing cybersecurity audits marks the start of your defensive evolution, not the finish line. Most business owners feel overwhelmed when handed a 60-page technical report filled with red flags and vulnerabilities. We eliminate that anxiety by translating complex jargon into a prioritized action plan. Our team categorizes findings into immediate threats and long-term strategic improvements. Statistics from the 2023 Verizon Data Breach Investigations Report show that 74% of all breaches involve a human element or privilege misuse. We focus on these high-risk areas first to provide the fastest return on your security investment.
The Telx Computers advantage lies in how we integrate these audit findings into our managed IT services in Miami. We don’t just hand you a list of problems; we become the engine that fixes them. By moving from a one-time checkup to a culture of continuous security, your business stays ahead of emerging threats like zero-day exploits and sophisticated phishing campaigns.
Building a Strategic Remediation Roadmap
We view every vulnerability discovered during an audit as an opportunity to modernize your infrastructure. If your report highlights aging hardware or sluggish protocols, our it management services turn those weaknesses into a streamlined, scalable environment. This proactive methodology prevents the recurring failures that plague businesses relying on “break-fix” models. You can request an instant quote today to begin transforming your audit results into a fortified digital roadmap.
- Immediate Remediation: Patching critical software gaps and enforcing multi-factor authentication.
- Strategic Upgrades: Transitioning to secure cloud environments and encrypted data storage.
- Compliance Alignment: Ensuring your systems meet the 2024 standards for HIPAA, PCI-DSS, or SOC2.
Securing Your Future with an Expert Guardian
True peace of mind comes from 24/7 server monitoring and the presence of a vigilant partner. When you work with local it companies in Miami, you gain a massive advantage in response time. While national providers might leave you in a support ticket queue for 12 hours, our local experts offer rapid intervention to stop threats in their tracks. We act as Your IT Department, providing the stable foundation your business needs to scale without fear. Don’t wait for a breach to expose your gaps. Secure your business today with a comprehensive Telx Computers audit and experience the confidence of total protection.
Fortify Your Miami Enterprise for 2026 and Beyond
Protecting your organization in 2026 demands a proactive stance that goes beyond standard firewalls. You’ve explored how localized cybersecurity audits provide the visibility needed to identify vulnerabilities before they’re exploited by emerging threats. By implementing our essential checklist and choosing the “Expert Guardian” approach, you transition from reactive fixes to a state of permanent readiness. Telx Computers brings 22 years of South Florida IT excellence to your side, ensuring your infrastructure meets the highest standards of compliance and performance.
We’ve built our reputation on being more than a service provider; we’re your dedicated IT department. With our 24/7 local Miami help desk and a deep commitment to regional business success, we remove the technical anxiety that holds many leaders back. It’s time to stop worrying about digital risks and start focusing on your next phase of growth. Secure your assets with a partner that’s been leading the South Florida landscape since 2002. We’re ready when you are.
Get Your Professional Cybersecurity Audit & Instant Quote Today
Let’s build a more secure future for your business together.
Frequently Asked Questions
How often should my Miami business undergo a cybersecurity audit?
Your Miami business should undergo a full cybersecurity audit at least once every 12 months. Companies in high-risk sectors like finance or healthcare often require these assessments every 6 months to maintain security. The 2023 IBM Data Breach Report found that organizations with high levels of security AI and automation saved $1.76 million compared to those without. Regular scheduling ensures your defenses evolve alongside emerging threats.
What is the difference between a vulnerability scan and a full cybersecurity audit?
A vulnerability scan is an automated tool that identifies known security gaps, while a full audit is a comprehensive manual review of your entire digital infrastructure. Scans typically check for the 200,000 entries currently listed in the National Vulnerability Database. In contrast, cybersecurity audits examine your internal policies, employee training, and physical security measures. Think of a scan as a quick check of your locks and an audit as a full inspection of your building’s structural integrity.
Will a cybersecurity audit disrupt my employees during the workday?
A professional audit won’t disrupt your daily operations or slow down your employees. We perform 90 percent of the technical assessment in the background using non-intrusive scanning tools and off-peak data analysis. Your team continues their work while we verify your systems. We schedule the brief interviews required for policy review at your convenience to ensure zero downtime for your critical business processes.
Does my small business in Fort Lauderdale really need a formal audit?
Every Fort Lauderdale business needs a formal audit regardless of its size. The Small Business Administration reports that 43 percent of all cyberattacks target small enterprises, yet only 14 percent of these companies have a plan to defend themselves. Small firms often serve as entry points for hackers looking to access larger supply chains. A proactive audit protects your local reputation and ensures you aren’t the weakest link in your professional network.
What are the specific Florida laws regarding data breach notification?
The Florida Information Protection Act (FIPA), enacted in 2014, governs your legal obligations. You must notify the Florida Department of Legal Affairs of any breach affecting 500 or more individuals within 30 days of discovery. Failure to comply can result in administrative fines of $1,000 per day for the first 30 days. We help you implement the technical controls required to meet these strict statutory deadlines and avoid costly penalties.
How much does a professional cybersecurity audit cost for a mid-sized firm?
A professional audit for a mid-sized firm typically ranges from $10,000 to $30,000 depending on your network complexity. This investment covers a 50 person office with standard server configurations and cloud integrations. While the upfront cost is a factor, it’s a fraction of the $164 per-record cost associated with data breaches in 2023. We provide a tailored quote based on your specific headcount and regulatory requirements to ensure maximum value.
Can an audit help my business meet HIPAA or SOC 2 compliance requirements?
An audit is the primary tool for achieving and maintaining HIPAA or SOC 2 compliance. For healthcare providers, we verify the 18 protected health information (PHI) identifiers are encrypted according to federal standards. If you’re pursuing SOC 2 Type II, cybersecurity audits provide the necessary evidence for the 6 to 12 month observation period required by auditors. We align our technical checks with these specific frameworks to streamline your certification process.
What happens if the audit finds significant vulnerabilities in our network?
We provide a prioritized remediation roadmap that ranks every finding by its risk level. Each vulnerability is categorized as Critical, High, Medium, or Low based on the CVSS 3.1 scoring system. You won’t just get a list of problems; you’ll receive a clear action plan to fix them. Our team works as your strategic ally to patch these holes, ensuring your business returns to a secure and stable state immediately.




